使用S3 Browser演示,存储桶策略允许您创建条件规则,以管理对存储桶和文件的访问。通过存储桶策略,还可以定义适用于多个文件的安全规则,包括存储桶中的所有文件或文件子集。这使得更新和管理权限变得更加容易!
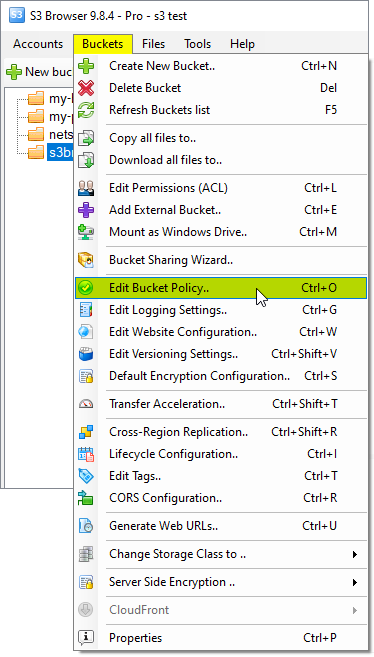
1. 点击存储桶(Buckets),编辑存储桶策略(Edit Bucket Policy)。你也可以使用快捷键Ctrl+O打开存储桶策略编辑器。
2. 打开存储桶策略编辑器(Bucket Policy Editor)对话框,存储桶策略编辑器允许您添加、编辑和删除存储桶策略。
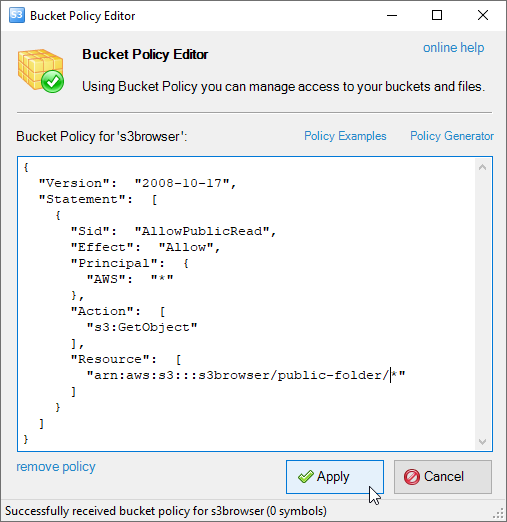
3. 输入有效的亚马逊S3存储桶策略,然后点击应用(Apply)存储桶策略。
请参阅下面的S3存储桶策略示例和访问策略语言参考以获取更多详细信息。
亚马逊S3存储桶策略示例
如何授予匿名用户(即所有人)公共读取权限
{
"Version": "2008-10-17",
"Statement": [
{
"Sid": "AllowPublicRead",
"Effect": "Allow",
"Principal": {
"AWS": "*"
},
"Action": [
"s3:GetObject"
],
"Resource": [
"arn:aws:s3:::my-brand-new-bucket/*"
]
}
]
}
如何授予特定IP地址用户的完全访问权限:
{
"Version": "2008-10-17",
"Id": "S3PolicyId1",
"Statement": [
{
"Sid": "IPAllow",
"Effect": "Allow",
"Principal": {
"AWS": "*"
},
"Action": "s3:*",
"Resource": "arn:aws:s3:::my-brand-new-bucket/*",
"Condition": {
"IpAddress": {
"aws:SourceIp": "192.168.143.0/24"
},
"NotIpAddress": {
"aws:SourceIp": "192.168.143.188/32"
}
}
},
{
"Sid": "IPDeny",
"Effect": "Deny",
"Principal": {
"AWS": "*"
},
"Action": "s3:*",
"Resource": "arn:aws:s3:::my-brand-new-bucket/*",
"Condition": {
"IpAddress": {
"aws:SourceIp": "10.1.2.0/24"
}
}
}
]
}
如何保护您的亚马逊S3文件免受热链接
{
"Version": "2008-10-17",
"Id": "preventHotLinking",
"Statement": [
{
"Sid": "1",
"Effect": "Allow",
"Principal": {
"AWS": "*"
},
"Action": "s3:GetObject",
"Resource": "arn:aws:s3:::my-brand-new-bucket/*",
"Condition": {
"StringLike": {
"aws:Referer": [
"http://yourwebsitename.com/*",
"http://www.yourwebsitename.com/*"
]
}
}
}
]
}
如何仅允许特定IP写入存储桶,而让所有人从中读取
{
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "*"
},
"Action": "s3:GetObject",
"Resource": "arn:aws:s3:::my-brand-new-bucket/*",
"Condition": {
}
},
{
"Effect": "Allow",
"Principal": {
"AWS": "*"
},
"Action": [
"s3:PutObject",
"s3:DeleteObject"
],
"Resource": "arn:aws:s3:::my-brand-new-bucket/*",
"Condition": {
"IpAddress": {
"aws:SourceIp": "192.168.0.0/16"
}
}
}
]
}